A new as-yet unpatched weakness in Apple's iCloud Private Relay feature could be circumvented to leak users' true IP addresses from iOS devices running the latest version of the operating system. Introduced with iOS 15, which was officially released this week, iCloud Private Relay aims to improve anonymity on the web by employing a dual-hop architecture that effectively shields … [Read more...] about Apple’s New iCloud Private Relay Service Leaks Users’ Real IP Addresses
Search Results for: clear dns cache os x
Linux Implementation of Cobalt Strike Beacon Targeting Organizations Worldwide
Researchers on Monday took the wraps off a newly discovered Linux and Windows re-implementation of Cobalt Strike Beacon that's actively set its sights on government, telecommunications, information technology, and financial institutions in the wild. The as-yet undetected version of the penetration testing tool — codenamed "Vermilion Strike" — marks one of the rare Linux ports, … [Read more...] about Linux Implementation of Cobalt Strike Beacon Targeting Organizations Worldwide
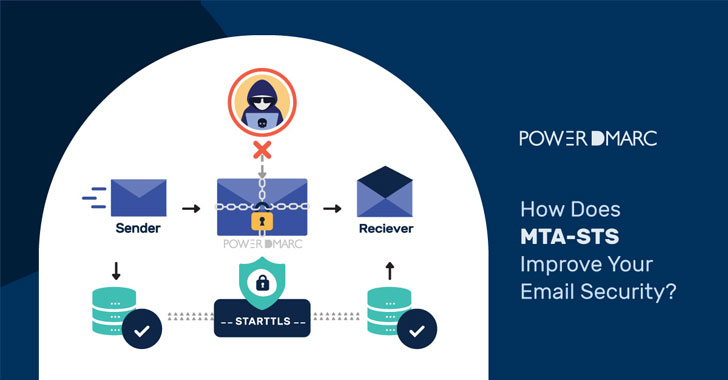
How Does MTA-STS Improve Your Email Security?
Simple Mail Transfer Protocol or SMTP has easily exploitable security loopholes. Email routing protocols were designed in a time when cryptographic technology was at a nascent stage (e.g., the de-facto protocol for email transfer, SMTP, is nearly 40 years old now), and therefore security was not an important consideration. As a result, in most email systems encryption is still … [Read more...] about How Does MTA-STS Improve Your Email Security?
A Visual Take on Email Authentication and Security
There is a saying that goes something like, "Do not judge a book by its cover." Yet, we all know we can not help but do just that - especially when it comes to online security. Logos play a significant role in whether or not we open an email and how we assess the importance of each message. Brand Indicators for Message Identification, or BIMI, aims to make it easier for us to … [Read more...] about A Visual Take on Email Authentication and Security
New Mirai-Inspired Botnet Could Be Using Your KGUARD DVRs in Cyber Attacks
Cybersecurity researchers on Thursday revealed details about a new Mirai-inspired botnet called "mirai_ptea" that leverages an undisclosed vulnerability in digital video recorders (DVR) provided by KGUARD to propagate and carry out distributed denial-of-service (DDoS) attacks. Chinese security firm Netlab 360 pinned the first probe against the flaw on March 23, 2021, before it … [Read more...] about New Mirai-Inspired Botnet Could Be Using Your KGUARD DVRs in Cyber Attacks
Cyber espionage by Chinese hackers in neighbouring nations is on the rise
A string of cyber espionage campaigns dating all the way back to 2014 and focused on gathering military intelligence from neighbouring countries have been linked to a Chinese military-intelligence apparatus. In a wide-ranging report published by Massachusetts-headquartered Recorded Future this week, the cybersecurity firm's Insikt Group said it identified ties between a group … [Read more...] about Cyber espionage by Chinese hackers in neighbouring nations is on the rise
Nearly All Wi-Fi Devices Are Vulnerable to New FragAttacks
Three design and multiple implementation flaws have been disclosed in IEEE 802.11 technical standard that undergirds Wi-Fi, potentially enabling an adversary to take control over a system and plunder confidential data. Called FragAttacks (short for FRgmentation and AGgregation attacks), the weaknesses impact all Wi-Fi security protocols, from Wired Equivalent Privacy (WEP) all … [Read more...] about Nearly All Wi-Fi Devices Are Vulnerable to New FragAttacks
New NAME:WRECK Vulnerabilities Impact Nearly 100 Million IoT Devices
Security researchers have uncovered nine vulnerabilities affecting four TCP/IP stacks impacting more than 100 million consumer and enterprise devices that could be exploited by an attacker to take control of a vulnerable system. Dubbed "NAME:WRECK" by Forescout and JSOF, the flaws are the latest in series of studies undertaken as part of an initiative called Project Memoria to … [Read more...] about New NAME:WRECK Vulnerabilities Impact Nearly 100 Million IoT Devices
New Mirai Variant and ZHtrap Botnet Malware Emerge in the Wild
Cybersecurity researchers on Monday disclosed a new wave of ongoing attacks exploiting multiple vulnerabilities to deploy Mirai variants on compromised systems. "Upon successful exploitation, the attackers try to download a malicious shell script, which contains further infection behaviors such as downloading and executing Mirai variants and brute-forcers," Palo Alto Networks' … [Read more...] about New Mirai Variant and ZHtrap Botnet Malware Emerge in the Wild
Google Will Use ‘FLoC’ for Ad Targeting Once 3rd-Party Cookies Are Dead
Signaling a major shift to its ads-driven business model, Google on Wednesday unequivocally stated it would not build alternate identifiers or tools to track users across multiple websites once it begins phasing out third-party tracking cookies from its Chrome browser by early 2022. "Instead, our web products will be powered by privacy-preserving APIs which prevent individual … [Read more...] about Google Will Use ‘FLoC’ for Ad Targeting Once 3rd-Party Cookies Are Dead