Dec 28, 2023NewsroomCloud Security / Data Protection Google Cloud has addressed a medium-severity security flaw in its platform that could be abused by an attacker who already has access to a Kubernetes cluster to escalate their privileges. "An attacker who has compromised the Fluent Bit logging container could combine that access with high privileges required by Anthos … [Read more...] about Google Cloud Resolves Privilege Escalation Flaw Impacting Kubernetes Service
Service
Istio Roadmap, Ambient Mesh, and the Service Mesh Landscape
In the dynamic landscape of microservices and cloud-native architectures, the role of service meshes has become increasingly crucial. These programmable frameworks empower users to seamlessly connect, secure, and observe their microservices, relieving them of the complexities associated with these critical tasks within their applications. Istio, a leading service mesh project, … [Read more...] about Istio Roadmap, Ambient Mesh, and the Service Mesh Landscape
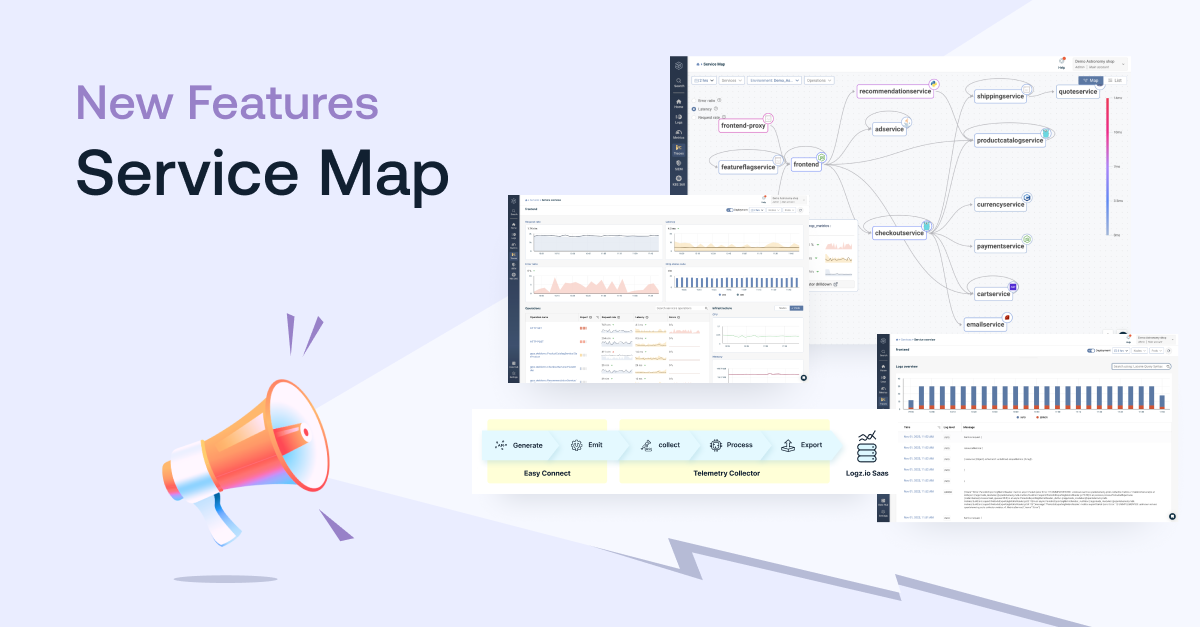
Announcing Service Map: Troubleshoot With Context and Confidence
Logz.io is excited to announce Service Map, a new way to visualize the data flow, dependencies, and critical performance metrics throughout your microservices architecture, which makes it easy to gather critical troubleshooting context as you investigate production issues.After sending your trace data to Logz.io Open 360™, Service Map automatically discovers and maps your … [Read more...] about Announcing Service Map: Troubleshoot With Context and Confidence
Play Ransomware Goes Commercial – Now Offered as a Service to Cybercriminals
Nov 21, 2023NewsroomRansomware-as-a-service The ransomware strain known as Play is now being offered to other threat actors "as a service," new evidence unearthed by Adlumin has revealed. "The unusual lack of even small variations between attacks suggests that they are being carried out by affiliates who have purchased the ransomware-as-a-service (RaaS) and are following … [Read more...] about Play Ransomware Goes Commercial – Now Offered as a Service to Cybercriminals
Researchers Uncover Wiretapping of XMPP-Based Instant Messaging Service
Oct 28, 2023NewsroomPrivacy / Data Security New findings have shed light on what's said to be a lawful attempt to covertly intercept traffic originating from jabber[.]ru (aka xmpp[.]ru), an XMPP-based instant messaging service, via servers hosted on Hetzner and Linode (a subsidiary of Akamai) in Germany. "The attacker has issued several new TLS certificates using Let's … [Read more...] about Researchers Uncover Wiretapping of XMPP-Based Instant Messaging Service
Falcon and Red Hat OpenShift Service on AWS (ROSA)
As organizations increasingly deploy business-critical workloads to managed cloud services, enforcing strong security practices needs to be a top priority. While many managed cloud service providers do a good job of protecting the cloud and infrastructure itself, it’s the responsibility of the customer to protect what’s running inside the cloud. This is commonly known as the … [Read more...] about Falcon and Red Hat OpenShift Service on AWS (ROSA)
Continuous Security Validation with Penetration Testing as a Service (PTaaS)
Validate security continuously across your full stack with Pen Testing as a Service. In today's modern security operations center (SOC), it's a battle between the defenders and the cybercriminals. Both are using tools and expertise – however, the cybercriminals have the element of surprise on their side, and a host of tactics, techniques, and procedures (TTPs) that have … [Read more...] about Continuous Security Validation with Penetration Testing as a Service (PTaaS)
AVRecon Botnet Leveraging Compromised Routers to Fuel Illegal Proxy Service
Jul 31, 2023THNNetwork Security / Botnet More details have emerged about a botnet called AVRecon, which has been observed making use of compromised small office/home office (SOHO) routers as part of a multi-year campaign active since at least May 2021. AVRecon was first disclosed by Lumen Black Lotus Labs earlier this month as malware capable of executing additional commands … [Read more...] about AVRecon Botnet Leveraging Compromised Routers to Fuel Illegal Proxy Service
Simplified Observability & Faster Time-to-Insights with Logz.io Service Overview
Logz.io is excited to announce Service Overview, a fast and easy way to unify telemetry data and insights across your infrastructure and applications into a single interface. Our Beta users have reported simplified observability, faster time-to-insights, and observability consolidation.The Business Case for Observability and Service OverviewAs digital interactions increasingly … [Read more...] about Simplified Observability & Faster Time-to-Insights with Logz.io Service Overview
Improving the Elastic APM UI performance with continuous rollups and service metrics
Our journey began back in the 7.x series where we noticed that doing ad-hoc aggregations on raw transaction data put Elasticsearch® under a lot of pressure in large-scale environments. Since then, we’ve begun to pre-aggregate the transactions into transaction metrics during ingestion. This has helped to keep the performance of the UI relatively stable. Regardless of how busy … [Read more...] about Improving the Elastic APM UI performance with continuous rollups and service metrics