Comprehensive cloud support is essential when agile and efficient security at scale is required. With Cisco Secure Firewall Threat Defense 7.1, we have added support for the AWS Gateway Load Balancer (GWLB) to drive simple, agile, and efficient security in the cloud. This integration simplifies insertion of Cisco Secure Firewall in AWS with Geneve protocol (RFC 8926) … [Read more...] about Building a Scalable Security Architecture on AWS with Cisco Secure Firewall and AWS Transit Gateway
building
Building Scalable Security with Cisco Secure Firewall Cloud Native Version 1.1
Today, companies invest in making their security controls scalable and dynamic to meet the ever-increasing demand for their network(s). In many cases, the response is a massive shift to Kubernetes® (K8s®) orchestrated infrastructure that provides a cloud-native, scalable, and resilient infrastructure. This is where Cisco Secure Firewall Cloud Native comes in, giving you the … [Read more...] about Building Scalable Security with Cisco Secure Firewall Cloud Native Version 1.1
Building Consumer Confidence Through Transparency and Control
Protecting privacy continues to be a critical issue for individuals, organizations, and governments around the world. Eighteen months into the COVID-19 pandemic, our health information and vaccination status are needed more than ever to understand the virus, control the spread, and enable safer environments for work, learning, recreation, and other activities. Nonetheless, … [Read more...] about Building Consumer Confidence Through Transparency and Control
Building a Custom SecureX Orchestration Workflow for Umbrella
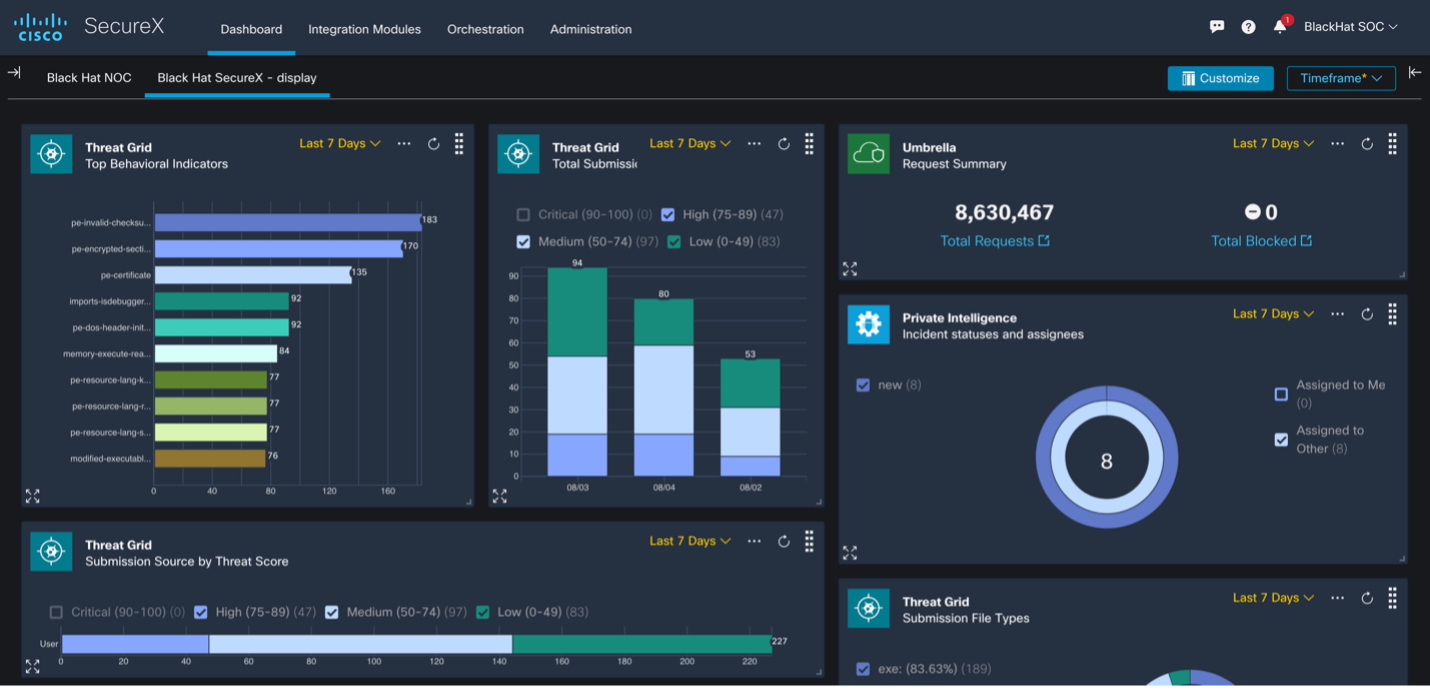
Improving efficiency for the Cisco team in the Black Hat USA NOC As a proud partner of the Black Hat USA NOC, Cisco deployed multiple technologies along with the other Black Hat NOC partners to build a stable and secure network for the conference. We used Cisco Secure Malware Analytics to analyze files and monitor any potential PII leaks. We also used Meraki SM to manage over … [Read more...] about Building a Custom SecureX Orchestration Workflow for Umbrella
Building a scalable RAVPN architecture in Oracle Cloud Infrastructure using Cisco Secure Firewall
Oracle Cloud Infrastructure (OCI) provides a wide range of cloud-computing services, workloads, and applications to organizations globally. With Cisco Secure Firewall, organizations are able to build a scalable RAVPN architecture on OCI, providing employees secure remote access to their organization’s resources from any location or endpoint. This scalable architecture brings … [Read more...] about Building a scalable RAVPN architecture in Oracle Cloud Infrastructure using Cisco Secure Firewall
Building trust through transparency and privacy by design
Privacy by design and default are principles that have been in the privacy engineering lexicon for decades, but only recently have come more broadly to light. These principles aren’t just recommendations or best practices anymore. Privacy by design and default are legally required of companies building products and services in or for the European Union market and other … [Read more...] about Building trust through transparency and privacy by design
Building a Culture of Security at Brunel University
This week in #EducationNow, join us as we battle threats and mitigate risks at Brunel University London with a team that brings diverse experience from the battlefield to the boardroom. What is culture? Merriam Webster defines it as “The set of shared attitudes, values, goals, and practices that characterizes an institution or organization.” When looking at an education … [Read more...] about Building a Culture of Security at Brunel University
3 Best Practices for Building a High-Performance Graph Database
CrowdStrike® employees like to say that there is big data, huge data and our data. To date, we have collected, analyzed and stored more than 15 petabytes of data, generated through hundreds of billions of daily security events. At the center of this massive data repository is CrowdStrike Threat Graph®, our custom-built, cutting-edge security analytics tool that collects … [Read more...] about 3 Best Practices for Building a High-Performance Graph Database
Israel Neutralizes Cyber Attack by Blowing Up Building with Jihadist Hackers
The Israel Defense Force (IDF) claims to have neutralized an "attempted" cyber attack by launching airstrikes on a building in Gaza Strip from where it says the attack was originated.As shown in a video tweeted by IDF, the building in the Gaza Strip, which Israeli fighter drones have now destroyed, was reportedly the headquarters for Palestinian Hamas military intelligence, … [Read more...] about Israel Neutralizes Cyber Attack by Blowing Up Building with Jihadist Hackers