Email is the top initial attack vector, with phishing campaigns responsible for many damaging cyber attacks, including ransomware. Being able to search Mimecast email security logs in CrowdStrike Falcon® LogScale (formerly known as Humio), alongside other log sources such as endpoint, network and authentication data helps cybersecurity teams detect and respond to cyber … [Read more...] about Mitigate Cyber Risk From Email With the Falcon LogScale and Mimecast Integration
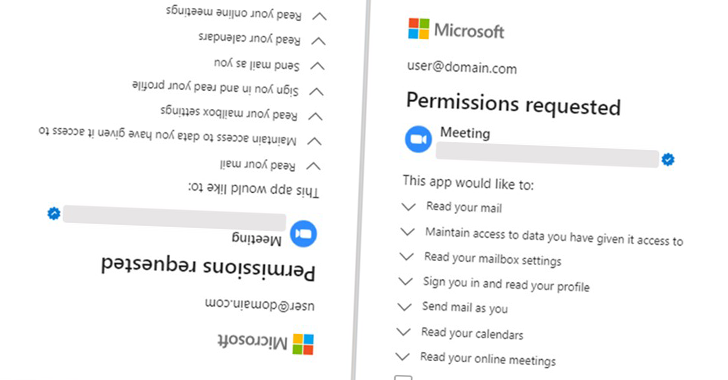
Hackers Abused Microsoft’s “Verified Publisher” OAuth Apps to Breach Corporate Email Accounts
Feb 01, 2023Ravie LakshmananEnterprise Security / Authentication Microsoft on Tuesday said it took steps to disable fake Microsoft Partner Network (MPN) accounts that were used for creating malicious OAuth applications as part of a malicious campaign designed to breach organizations' cloud environments and steal email. "The applications created by these fraudulent actors were … [Read more...] about Hackers Abused Microsoft’s “Verified Publisher” OAuth Apps to Breach Corporate Email Accounts
Understanding Business Email Compromise to better protect against it
What is business email compromise? Imagine this: Your CEO sends you an email asking for your help transferring $5,000 to a new vendor for an urgent project. You make the transfer, only to find out later that the email was actually from an imposter, and that money is now in the hands of cybercriminals. Oops, right? crickets Business Email Compromise (BEC) is a type of cybercrime … [Read more...] about Understanding Business Email Compromise to better protect against it
Secure Email Threat Defense: Providing critical insight into business risk
Attackers specifically craft business email compromise (BEC) and phishing emails using a combination of malicious techniques, expertly selected from an ever-evolving bag of tricks. They’ll use these techniques to impersonate a person or business that’s well-known to the targeted recipient and hide their true intentions, while attempting to avoid detection by security … [Read more...] about Secure Email Threat Defense: Providing critical insight into business risk
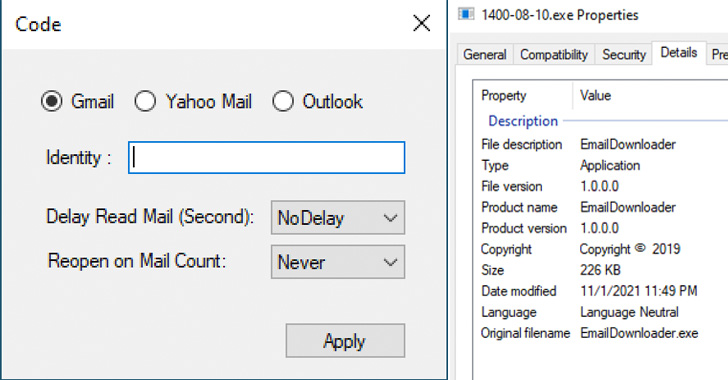
Google Uncovers Tool Used by Iranian Hackers to Steal Data from Email Accounts
The Iranian government-backed actor known as Charming Kitten has added a new tool to its malware arsenal that allows it to retrieve user data from Gmail, Yahoo!, and Microsoft Outlook accounts. Dubbed HYPERSCRAPE by Google Threat Analysis Group (TAG), the actively in-development malicious software is said to have been used against less than two dozen accounts in Iran, with the … [Read more...] about Google Uncovers Tool Used by Iranian Hackers to Steal Data from Email Accounts
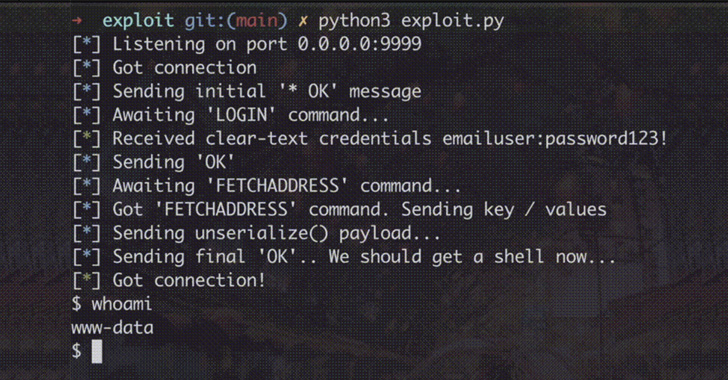
New Zimbra Email Vulnerability Could Let Attackers Steal Your Login Credentials
A new high-severity vulnerability has been disclosed in the Zimbra email suite that, if successfully exploited, enables an unauthenticated attacker to steal cleartext passwords of users sans any user interaction. "With the consequent access to the victims' mailboxes, attackers can potentially escalate their access to targeted organizations and gain access to various internal … [Read more...] about New Zimbra Email Vulnerability Could Let Attackers Steal Your Login Credentials
New Unpatched Horde Webmail Bug Lets Hackers Take Over Server by Sending Email
A new unpatched security vulnerability has been disclosed in the open-source Horde Webmail client that could be exploited to achieve remote code execution on the email server simply by sending a specially crafted email to a victim. "Once the email is viewed, the attacker can silently take over the complete mail server without any further user interaction," SonarSource said in a … [Read more...] about New Unpatched Horde Webmail Bug Lets Hackers Take Over Server by Sending Email
Hackers Hijack Email Reply Chains on Unpatched Exchange Servers to Spread Malware
A new email phishing campaign has been spotted leveraging the tactic of conversation hijacking to deliver the IcedID info-stealing malware onto infected machines by making use of unpatched and publicly-exposed Microsoft Exchange servers. "The emails use a social engineering technique of conversation hijacking (also known as thread hijacking)," Israeli company Intezer said in a … [Read more...] about Hackers Hijack Email Reply Chains on Unpatched Exchange Servers to Spread Malware
Hackers Exploited 0-Day Vulnerability in Zimbra Email Platform to Spy on Users
A threat actor, likely Chinese in origin, is actively attempting to exploit a zero-day vulnerability in the Zimbra open-source email platform as part of spear-phishing campaigns that commenced in December 2021. The espionage operation — codenamed "EmailThief" — was detailed by cybersecurity company Volexity in a technical report published Thursday, noting that successful … [Read more...] about Hackers Exploited 0-Day Vulnerability in Zimbra Email Platform to Spy on Users
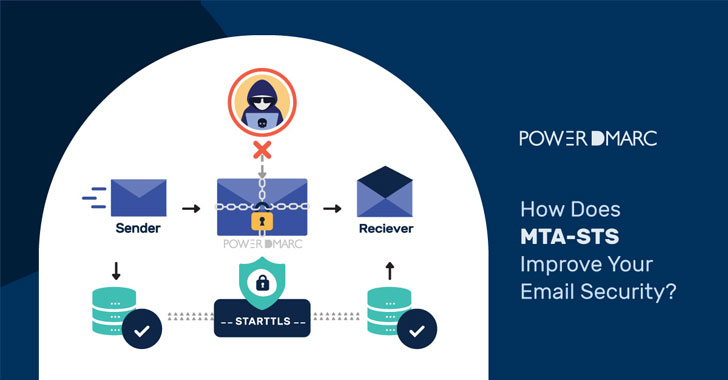
How Does MTA-STS Improve Your Email Security?
Simple Mail Transfer Protocol or SMTP has easily exploitable security loopholes. Email routing protocols were designed in a time when cryptographic technology was at a nascent stage (e.g., the de-facto protocol for email transfer, SMTP, is nearly 40 years old now), and therefore security was not an important consideration. As a result, in most email systems encryption is still … [Read more...] about How Does MTA-STS Improve Your Email Security?