This time last year, the CrowdStrike Falcon OverWatch™ reported on mounting cyber threats facing organizations as they raced to adopt work-from-home practices and adapt to constraints imposed by the rapidly escalating COVID-19 crisis. Unfortunately, the 12 months that followed have offered little in the way of reprieve for defenders. The past year has been marked by some of the … [Read more...] about A Peek Inside the 2021 Threat Hunting Report
Hunting
Big Game Hunting TTPs Continue to Shift After DarkSide Pipeline Attack
The eCrime ecosystem is an active and diverse economy of financially motivated threat actors engaging in a myriad of criminal activities to generate revenue. With the CrowdStrike eCrime Index (ECX), CrowdStrike’s Intelligence team maintains a composite score to track changes to this ecosystem. The ECX is composed of several key observables covering different aspects of … [Read more...] about Big Game Hunting TTPs Continue to Shift After DarkSide Pipeline Attack
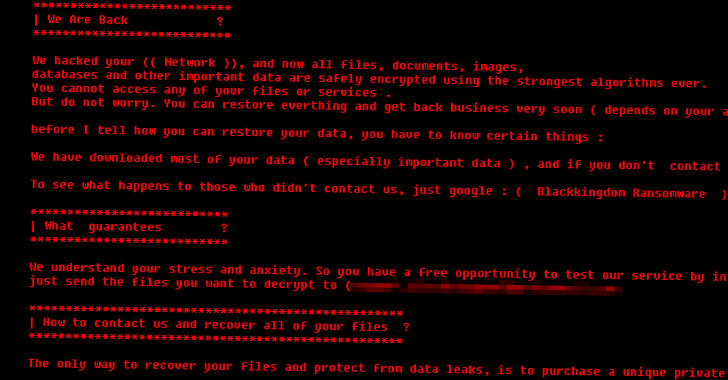
Black Kingdom Ransomware Hunting Unpatched Microsoft Exchange Servers
More than a week after Microsoft released a one-click mitigation tool to mitigate cyberattacks targeting on-premises Exchange servers, the company disclosed that patches have been applied to 92% of all internet-facing servers affected by the ProxyLogon vulnerabilities. The development, a 43% improvement from the previous week, caps off a whirlwind of espionage and malware … [Read more...] about Black Kingdom Ransomware Hunting Unpatched Microsoft Exchange Servers
Democratizing Threat Hunting: How to Make it Happen for Everyone
A report for everyone at every level of security, the Security Outcomes Study was released in December. In the report, we surveyed more than 4,800 IT, security and privacy professionals to find out what matters most in their security practice. Topics such as tech refresh, risk management, and incident response were examined from the perspective of a roadmap for success in an … [Read more...] about Democratizing Threat Hunting: How to Make it Happen for Everyone
Duck Hunting w/Falcon Complete Pt. 1: QakBot Malware Overview
Adversaries constantly develop new tactics that enhance their capabilities to deploy malware across networked environments and monetize infected systems. This blog is Part 1 of a three-part series detailing research and observations by the CrowdStrike® Falcon Complete™ managed services team regarding one such malware variant, QakBot (aka QBot), and its behavior in recent … [Read more...] about Duck Hunting w/Falcon Complete Pt. 1: QakBot Malware Overview
Highlights From 2020 Threat Hunting Report
CrowdStrike® Falcon OverWatch™ has released its new report, 2020 Threat Hunting Report: Insights from the CrowdStrike Falcon OverWatch Team. Now in its third year, this report continues to pull back the curtain on the daily battle being waged between Falcon OverWatch’s industry-leading threat hunting team and today’s highly motivated adversaries. Armed with cloud-scale … [Read more...] about Highlights From 2020 Threat Hunting Report
PowerShell Hunting with CrowdStrike Falcon
Introduction Threat hunting is the active search for new and novel attack behaviors that aren’t detected by current automated methods of prevention and detection. Threat hunting starts with human analysts, who approach their challenge with the assumption that active intrusions are underway but hidden from the view of their layers of detection technology such as NGAV, network … [Read more...] about PowerShell Hunting with CrowdStrike Falcon
Intelligence, Modelling and Hunting Through an ATT&CKers Lens
Unless you’ve been asleep recently, you’ll probably be aware of MITRE’s ATT&CK framework. This is a game changer for defenders as it maps out the common threats that an enterprise will face. ATT&CK aligns this to protective and detective controls and allows everyone within the enterprise to speak a common language on how attackers might move through an infrastructure. … [Read more...] about Intelligence, Modelling and Hunting Through an ATT&CKers Lens
WastedLocker Goes “Big-Game Hunting” in 2020
By Ben Baker, Edmund Brumaghin, JJ Cummings and Arnaud Zobec. Threat summary After initially compromising corporate networks, the attacker behind WastedLocker performs privilege escalation and lateral movement prior to activating ransomware and demanding ransom payment. The use of “dual-use” tools and “LoLBins” enables adversaries to evade detection and stay under the radar as … [Read more...] about WastedLocker Goes “Big-Game Hunting” in 2020
THREAT HUNTING WITH A REMOTE WORKFORCE
Introduction In the world of cybersecurity, adversaries and defenders are constantly trying to outmaneuver each other and gain strategic advantage. For example, attackers are keenly aware that the shift to work-from-home has placed tremendous pressure on security teams and realize that now is the time to exploit potential infrastructure and security gaps caused by this … [Read more...] about THREAT HUNTING WITH A REMOTE WORKFORCE