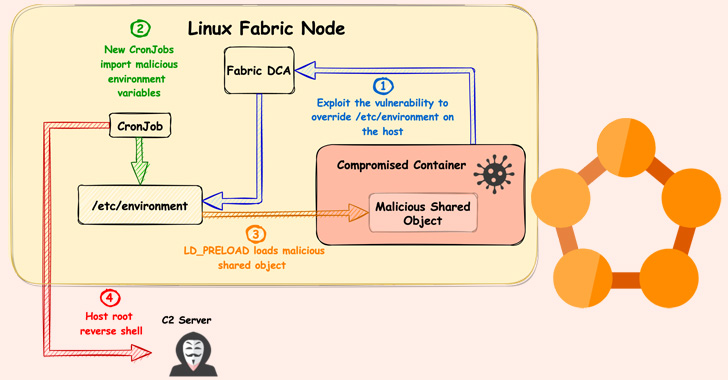
Cybersecurity researchers from Palo Alto Networks Unit 42 disclosed details of a new security flaw affecting Microsoft's Service Fabric that could be exploited to obtain elevated permissions and seize control of all nodes in a cluster. The issue, which has been dubbed FabricScape (CVE-2022-30137), could be exploited on containers that are configured to have runtime access. It … [Read more...] about New ‘FabricScape’ Bug in Microsoft Azure Service Fabric Impacts Linux Workloads
Linux
A New Golang-based Peer-To-Peer Botnet Targeting Linux Servers
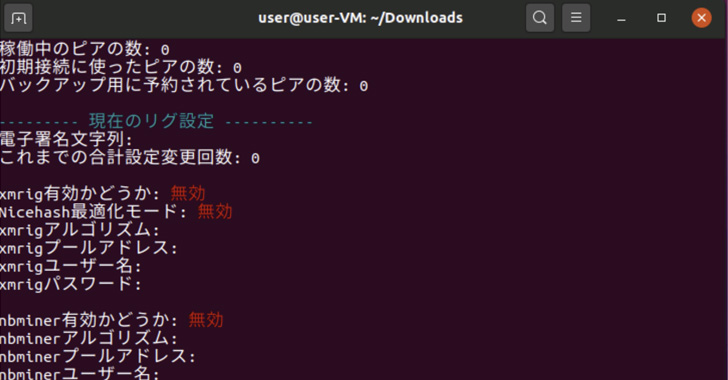
A new Golang-based peer-to-peer (P2P) botnet has been spotted actively targeting Linux servers in the education sector since its emergence in March 2022. Dubbed Panchan by Akamai Security Research, the malware "utilizes its built-in concurrency features to maximize spreadability and execute malware modules" and "harvests SSH keys to perform lateral movement." The … [Read more...] about A New Golang-based Peer-To-Peer Botnet Targeting Linux Servers
A Stealthy Linux Malware Targeting Latin American Financial Sector
Cybersecurity researchers have taken the wraps off what they call a "nearly-impossible-to-detect" Linux malware that could be weaponized to backdoor infected systems. Dubbed Symbiote by threat intelligence firms BlackBerry and Intezer, the stealthy malware is so named for its ability to conceal itself within running processes and network traffic and drain a victim's resources … [Read more...] about A Stealthy Linux Malware Targeting Latin American Financial Sector
New “B1txor20” Linux Botnet Uses DNS Tunnel and Exploits Log4J Flaw
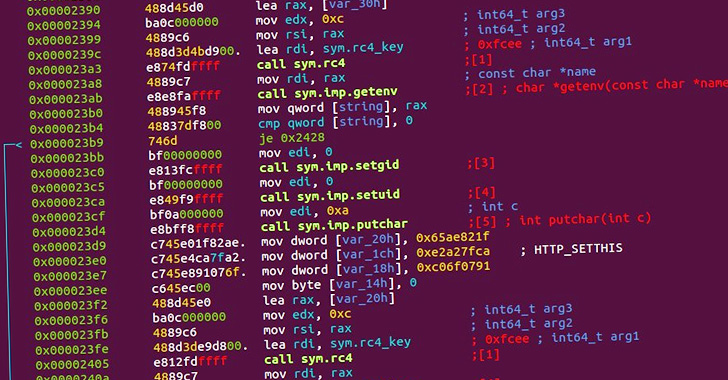
A previously undocumented backdoor has been observed targeting Linux systems with the goal of corralling the machines into a botnet and acting as a conduit for downloading and installing rootkits. Qihoo 360's Netlab security team called it B1txor20 "based on its propagation using the file name 'b1t,' the XOR encryption algorithm, and the RC4 algorithm key length of 20 … [Read more...] about New “B1txor20” Linux Botnet Uses DNS Tunnel and Exploits Log4J Flaw
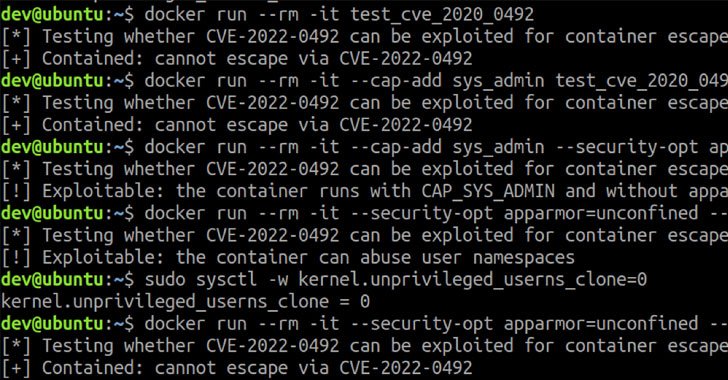
New Linux Kernel cgroups Vulnerability Could Let Attackers Escape Container
Details have emerged about a now-patched high-severity vulnerability in the Linux kernel that could potentially be abused to escape a container in order to execute arbitrary commands on the container host. The shortcoming resides in a Linux kernel feature called control groups, also referred to as cgroups version 1 (v1), which allows processes to be organized into hierarchical … [Read more...] about New Linux Kernel cgroups Vulnerability Could Let Attackers Escape Container
Hunting pwnkit (CVE-2021-4034) in Linux
In November 2021, a vulnerability was discovered in a ubiquitous Linux module named Polkit. Developed by Red Hat, Polkit facilitates the communication between privileged and unprivileged processes on Linux endpoints. Due to a flaw in a component of Polkit — pkexec — a local privilege escalation vulnerability exists that, when exploited, will allow a standard user to elevate to … [Read more...] about Hunting pwnkit (CVE-2021-4034) in Linux
Kubernetes Container Escape Using Linux Kernel Exploit
On Jan. 18, 2022, researchers found a heap base buffer overflow flaw (CVE-2022-0185) in the Linux kernel (5.1-rc1+) function “legacy_parse_param” of filesystem context functionality, which allows an out-of-bounds write in kernel memory. Using this primitive, an unprivileged attacker can escalate its privilege to root, bypassing any Linux namespace restrictions. CVE-2022-0185 … [Read more...] about Kubernetes Container Escape Using Linux Kernel Exploit
How to Extract Memory Information to Spot Linux Malware
Threat actors go to great lengths to hide the intentions of the malware they produce This blog demonstrates reliable methods for extracting information from popular Linux shells Extracted memory information can help categorize unknown software as malicious or benign and could reveal information to help incident responders Some malware is only ever resident in memory, so memory … [Read more...] about How to Extract Memory Information to Spot Linux Malware
New Golang-based Linux Malware Targeting eCommerce Websites
Weaknesses in e-commerce portals are being exploited to deploy a Linux backdoor as well as a credit card skimmer that's capable of stealing payment information from compromised websites. "The attacker started with automated e-commerce attack probes, testing for dozens of weaknesses in common online store platforms," researchers from Sansec Threat Research said in an analysis. … [Read more...] about New Golang-based Linux Malware Targeting eCommerce Websites
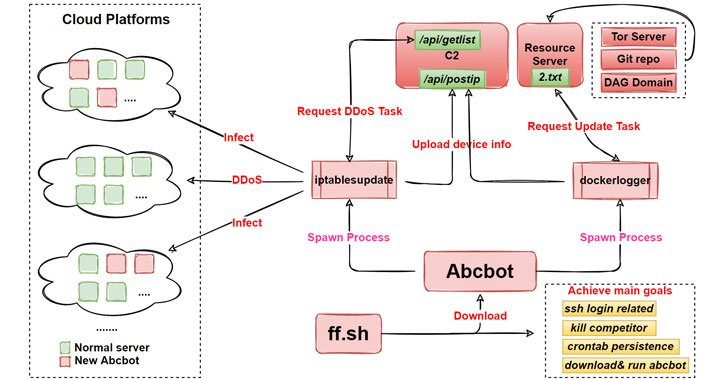
Abcbot — A New Evolving Wormable Botnet Malware Targeting Linux
Researchers from Qihoo 360's Netlab security team have released details of a new evolving botnet called "Abcbot" that has been observed in the wild with worm-like propagation features to infect Linux systems and launch distributed denial-of-service (DDoS) attacks against targets. While the earliest version of the botnet dates back to July 2021, new variants observed as recently … [Read more...] about Abcbot — A New Evolving Wormable Botnet Malware Targeting Linux