As the business environment becomes increasingly connected, organizations' attack surfaces continue to expand, making it challenging to map and secure both known and unknown assets. In particular, unknown assets present security challenges related to shadow IT, misconfigurations, ineffective scan coverage, among others. Given attack surface sprawl and evolving threats, many … [Read more...] about How Attack Surface Management Prioritizes Vulnerability Remediation
Management
Why Now? The Rise of Attack Surface Management
Jun 12, 2023The Hacker NewsAttack Surface Management The term "attack surface management" (ASM) went from unknown to ubiquitous in the cybersecurity space over the past few years. Gartner and Forrester have both highlighted the importance of ASM recently, multiple solution providers have emerged in the space, and investment and acquisition activity have seen an uptick. Many … [Read more...] about Why Now? The Rise of Attack Surface Management
5 Reasons Why Access Management is the Key to Securing the Modern Workplace
The way we work has undergone a dramatic transformation in recent years. We now operate within digital ecosystems, where remote work and the reliance on a multitude of digital tools is the norm rather than the exception. This shift – as you likely know from your own life – has led to superhuman levels of productivity that we wouldn't ever want to give up. But moving fast comes … [Read more...] about 5 Reasons Why Access Management is the Key to Securing the Modern Workplace
How Attack Surface Management Supports Continuous Threat Exposure Management
May 11, 2023The Hacker News According to Forrester, External Attack Surface Management (EASM) emerged as a market category in 2021 and gained popularity in 2022. In a different report, Gartner concluded that vulnerability management vendors are expanding their offerings to include Attack Surface Management (ASM) for a suite of comprehensive offensive security … [Read more...] about How Attack Surface Management Supports Continuous Threat Exposure Management
The power of effective log management in software development and operations
,The rapid software development process that exists today requires an expanding and complex infrastructure and application components, and the job of operations and development teams is ever growing and multifaceted. Observability, which helps manage and analyze telemetry data, is the key to ensuring the performance and reliability of your applications and infrastructure. In … [Read more...] about The power of effective log management in software development and operations
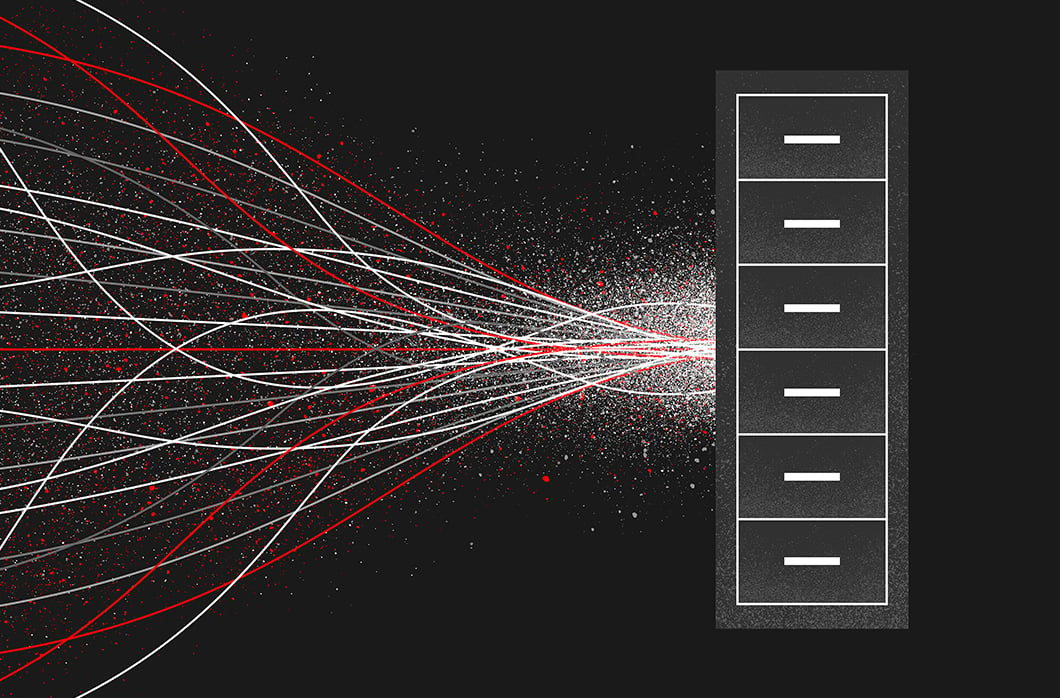
Centralized Log Management Best Practices and Tools
What is centralized log management? And why bother?Centralized logging is a critical component of observability into modern infrastructure and applications. Without it, it can be difficult to diagnose problems and understand user journeys—leaving engineers blind to production incidents or interrupted customer experiences. Alternatively, when the right engineers can access the … [Read more...] about Centralized Log Management Best Practices and Tools
Make Compliance a Breeze with Modern Log Management
From manufacturers in Michigan to fintechs in Finland, every business must comply with industry regulations — which are increasingly constraining. At the same time, businesses must protect and account for a growing number of systems, applications and data in order to remain compliant. In other words, compliance is getting harder. Enter log management. While regulations vary by … [Read more...] about Make Compliance a Breeze with Modern Log Management
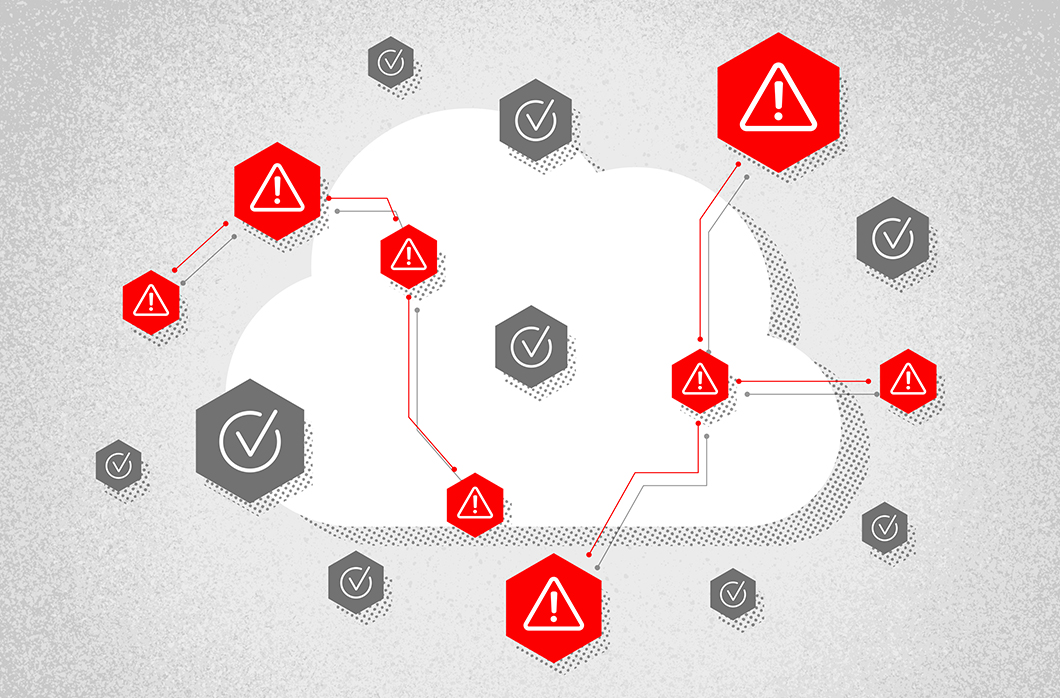
3 Ways Visualization Improves Cloud Asset Management and Security
Public cloud services and cloud assets are agile and dynamic environments. Close oversight of these assets is a critical component of your asset management and security practices. While it’s important to understand the relationships and potential vulnerabilities of your cloud assets, the practice of managing these systems is complicated by the ever-changing nature of cloud … [Read more...] about 3 Ways Visualization Improves Cloud Asset Management and Security
Make Compliance a Breeze with Modern Log Management
From manufacturers in Michigan to fintechs in Finland, every business must comply with industry regulations — which are increasingly constraining. At the same time, businesses must protect and account for a growing number of systems, applications and data in order to remain compliant. In other words, compliance is getting harder. Enter log management. While regulations vary by … [Read more...] about Make Compliance a Breeze with Modern Log Management
Making the most of your unstructured log data through enterprise log management
As we mentioned before, this is the single most important step for indexing custom logs. Technically these fixes are optional, but doing so allows you to get the most value from your unstructured logs. The log messages themselves are still unstructured and could contain anything — logs of text, numbers, expectations, errors, you name it.If you expand and review one of your log … [Read more...] about Making the most of your unstructured log data through enterprise log management